NexGenomics AI Fabric — Security Architecture
Overview
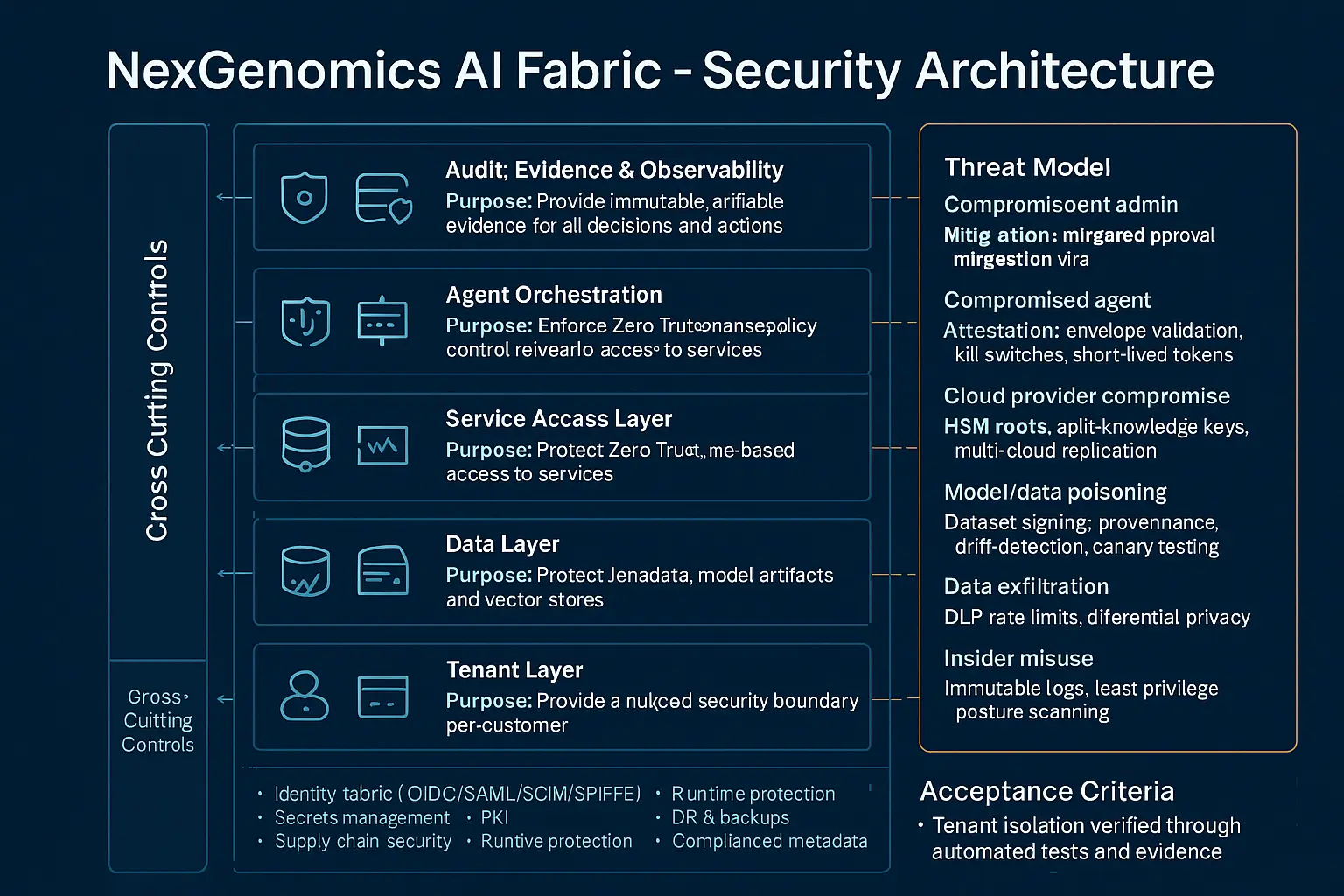
The NexGenomics AI Fabric is built on a seven‑layer security and governance architecture that ensures every action human, agent, or model is authenticated, authorized, auditable, and reversible. Controls are identity‑anchored, policy‑enforced, and produce immutable evidence across the entire platform. The design supports regulated industries, multi‑tenant isolation, and consequence‑aware AI operations.
Cross‑Cutting Controls (Apply Everywhere)
- Unified identity fabric (OIDC, SAML, SCIM, SPIFFE)
- Secrets management + short‑lived credentials
- PKI with HSM‑backed roots and automated rotation
- Supply chain security (SBOMs, signing, SCA/SAST/DAST)
- Runtime protection (container/host/GPU isolation)
- Vulnerability management + red‑team exercises
- DR and encrypted backups with tested RTO/RPO
- Data residency + regulatory metadata enforcement
- Security SLOs (policy latency, drift detection, key rotation)
Layered Architecture
- Audit, Evidence & Observability
- Purpose: Provide immutable, verifiable evidence for all decisions and actions.
- Key Controls: Append‑only signed logs, causal tracing, strict RBAC, evidence export APIs, SIEM integration, controlled auditor access.
Agent Orchestration
Purpose: Govern agent behavior and enforce policy at runtime.
Key Controls: Signed policy bundles, human approval gates, canary + rollback, orchestration attestation, operator escalation paths.
Agent Layer
Purpose: Execute data integration, inference, and actuation safely.
Key Controls: Agent attestation (TPM/SEV), scoped authority, short‑lived tokens, runtime integrity checks, GPU/CPU isolation, kill switches.
Service Access Layer
Purpose: Enforce Zero Trust, name‑based access to services.
Key Controls: SPIFFE/SPIRE identities, mTLS, PDP/PEP authorization, signed service registry, rate limits.
Data Layer
Purpose: Protect tenant data, model artifacts, and vector stores.
Key Controls: Envelope encryption, mTLS, tokenization/masking, ephemeral credentials, ABAC/RBAC, provenance, DLP (inputs + outputs), privacy controls.
Tenant Layer
Purpose: Provide a hard, cloud‑native security boundary per customer.
Key Controls: Policy‑driven provisioning, separate accounts/KMS/logs, separation of duties, quotas + cost governance, secure lifecycle APIs.
Cloud Infrastructure & Services
Purpose: Hardened multi‑cloud foundation with strong isolation.
Key Controls: Privileged admin agent, SSO + MFA, secure IaC bootstrap, KMS/HSM with split‑knowledge, immutable images, micro segmentation, CSPM.
Threat Model (Board‑Level View)
- Compromised tenant admin: mitigated via separation of duties, multi‑party approval, attestation.
- Compromised agent: mitigated via attestation, envelope validation, kill switches, short‑lived tokens.
- Cloud provider compromise: mitigated via HSM roots, split‑knowledge keys, multi‑cloud replication.
- Model/data poisoning: mitigated via dataset signing, provenance, drift detection, canary testing.
- Data exfiltration: mitigated via DLP, rate limits, differential privacy.
- Insider misuse: mitigated via immutable logs, least privilege, posture scanning.
What this Architecture Guarantees
- Tenant isolation is provable and testable.
- Every action is attributable and auditable.
- Agents cannot exceed their authority without detection.
- Data lineage and provenance are cryptographically verifiable.
- Policy changes are controlled, reversible, and evidenced.
- The platform is resilient to cloud, agent, and supply‑chain compromise.
Acceptance Criteria (Executive Level)
- Tenant isolation verified through automated tests and evidence.
- Signed audit trails with causal tracing across all layers.
- Agent attestation + emergency revoke functioning end‑to‑end.